Artur Ekert, University of Oxford – Crytographic Key Security
Every day, there are new reports of identity theft and other security breaches.
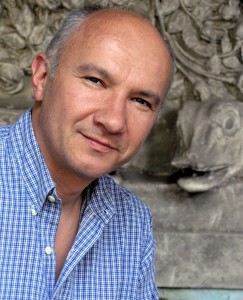
Artur Ekert, Professor of Quantum Physics at the Mathematical Institute at the University of Oxford, is studying cryptography and improving security systems.
Artur Ekert is Director of the Centre for Quantum Technologies and Lee Kong Chian Centennial Professor at the National University of Singapore. Dr. Ekert is also Professor of Quantum Physics at the Mathematical Institute, University of Oxford, UK. He is one of the co-inventors of quantum cryptography, and his current research extends over most aspects of information processing in quantum-mechanical systems. He has worked with and advised several companies and government agencies. He is a recipient of several awards, including the 1995 Maxwell Medal and Prize by the Institute of Physics and the 2007 Royal Society Hughes Medal. In his non-academic life, he is an avid scuba diver and pilot.
Artur Ekert – Cryotographic Key Security
Can you keep a secret? I mean, can we really keep anything secret at all, when we know the government is snooping and that code-makers have time and again been beaten by code-breakers?
Surprisingly, privacy is possible even if you are surrounded by the most powerful adversaries you can possibly imagine. All you need is a simple encryption method known as the one-time pad. It works like this. You take a sequence of random bits – just a list of ones and zeroes – and call this your cryptographic key. You convert your message into ones and zeroes too, like the codes inside computers, then, bit by bit, you add the key to your message. The random bits scramble the bits of the message. The result is easily deciphered by someone having the same cryptographic key, but is uncrackable to everyone else.
So, the problem is – how do we make and share such keys securely? In 1991, I proposed that we could use the quantum properties of photons, the particles of light. The quantum nature of photons creates randomness and can also reveal eavesdropping attempts. My scheme used pairs of entangled photons. Entanglement is a correlation in the photons’ behaviour– what Einstein called a “spooky action at a distance”.
It turns out these correlations are even more powerful for cryptography than I originally thought. My colleagues have improved upon my idea, showing that as long as you can verify the strength of the correlations, you don’t need to trust anything else about the devices. You could even buy them from your enemy! No matter if your enemy has superior quantum technology, or even post-quantum technology, you could keep your secrets secret. Even if your enemy were manipulating you a little, your message is safe.
Is it practical? Quantum key distribution is not just an academic curiosity. You can already buy devices that do a more simple form, that doesn’t use correlations. And this other kind? In research labs, the technology is almost there.
Read More: The Ultimate Physical Limits of Privacy


